Please Note:
The support ticket system is for technical questions and post-sale issues.
If you have pre-sale questions please use our chat feature or email information@mile2.com .
By Dr. Raymond Friedman – November 24, 2025
Why Behavioral Compliance, Not Technology, Is Now the #1 Factor in Cybersecurity Resilience.
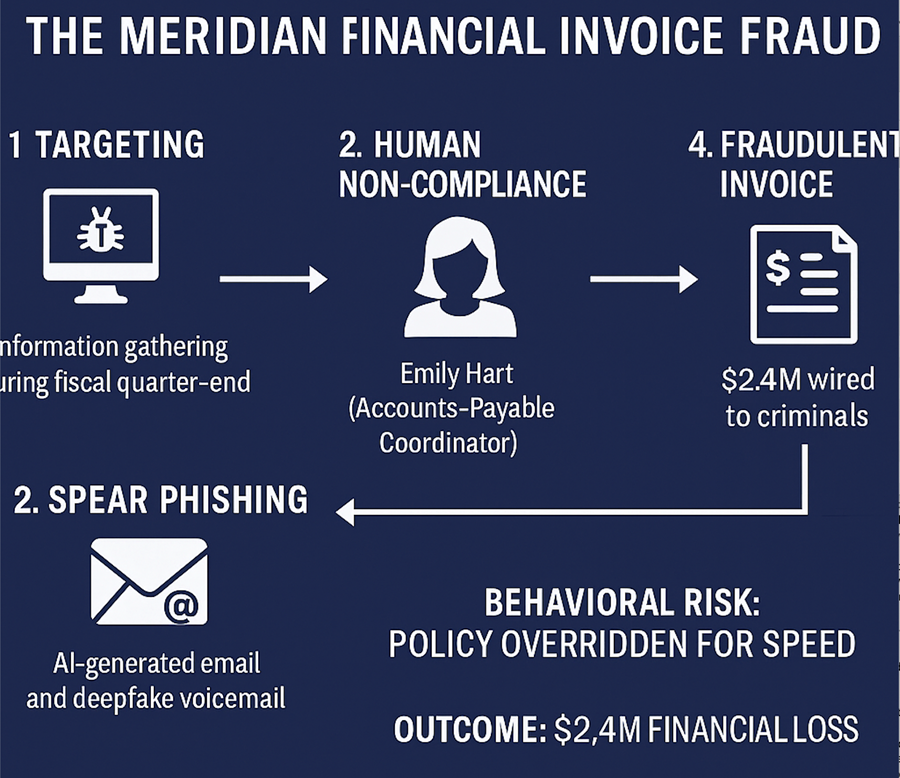
In March 2025, a company, for anonymity, identified as Meridian Financial Services (MFS) — a mid-sized lending and wealth management firm — experienced a catastrophic $2.4 million invoice redirection breach.
The attackers employed advanced AI-driven deception, domain spoofing, and voice cloning to execute a nearly flawless attempt at fraud. But the breach didn’t succeed because their tools/polices failed. It succeeded because an employee bypassed a single internal control. A mandatory verification step — ignored. A compliance reminder — dismissed. An attacker requests — trusted. This pattern is shockingly common.
Global studies reveal what most executives don’t want to admit:
Organizations continue to invest in better firewalls, zero-trust tools, and AI monitoring — yet they lack visibility into the behavioral readiness of their own workforce. This is precisely why Meridian fell. Because internal controls only work if people do.
A senior accounts payable coordinator, for anonymity, is referenced as Emily Hart, and received what appeared to be a standard vendor update request. She:
And just like that, $2.4M was transferred to a fraudulent overseas account. This wasn’t a zero-day exploit. It wasn’t a system misconfiguration. It wasn’t a failed tool. It was behavioral non-compliance — the most predictable cyber vulnerability.
After the breach, Meridian implemented the Behavioral Compliance Aptitude Assessment (BCAA™). The results were startling:
Department BCAA Averages Across 312 Employees:
Emily’s individual scores:
These scores placed her directly into the Compliance Risk Zone — meaning her behavioral profile already aligned with known patterns of policy bypass, shortcut-taking, and procedural drift. In other words: This breach was predictable. And preventable.
Organizations have perfected detection, automation, access controls, and monitoring…But none of that prevents an employee from:
Recent threat data shows:
AI isn’t attacking our firewalls. AI is attacking organizational staff. And unless organizations measure, correct, and reinforce employee behavior, breaches like Meridian’s will continue to rise — regardless of the level of security spending.
The Behavioral Compliance Aptitude Assessment (BCAA™) is a scientifically designed instrument that measures the human factors behind cybersecurity and compliance risk. Instead of evaluating technical skill, the BCAA™ analyzes organizational culture alignment, employee adherence behaviors, and ethical decision-making—the three dimensions most strongly linked to policy violations and control failures. By identifying individuals and teams with elevated behavioral risk, the BCAA™ provides organizations with early insight into who is most vulnerable to shortcuts, social engineering, and non-compliant actions, enabling targeted training, supervision, and governance before a breach occurs. The BCAA™ is the first behavioral analytics instrument explicitly designed for:
The BCAA™ transforms “soft factors” into measurable, actionable risk intelligence.
And perhaps most importantly, it quantifies the human attack surface — the part of cybersecurity that no technology can patch.
Industrywide data shows:
The cost of employee non-adherence is now greater than the cost of ransomware. Meridian learned this the hard way.
Meridian Financial did not lack tools, funding, or policies; what they lacked was visibility into behavior. The BCAA™ provides what every organization needs: An early warning system for behavioral cybersecurity risk.
The breach Meridian suffered could have been prevented months in advance — had the organization known who was most likely to bypass controls, why it was happening, and where cultural weaknesses existed. In an AI-driven threat landscape, behavior is the new perimeter — and the BCAA™ is the only instrument that measures it.
Cybersecurity and Infrastructure Security Agency. (2024). Ransomware Vulnerability Warning Pilot: Key findings report. CISA. https://www.cisa.gov/resources-tools/resources/ransomware
HP Wolf Security. (2023). Blurring boundaries & blind spots report. HP Development Company. https://www.hp.com/us-en/security/enterprise-security/wolf-security.html
Tessian. (2024). The state of data loss report. Tessian Cybersecurity Research. https://www.tessian.com/resources/state-of-data-loss-report/
Tessian, & Stanford University. (2022). The psychology of human error. Tessian Research. https://www.tessian.com/research/the-psychology-of-human-error/
SlashNext. (2024). 2024 Phishing intelligence report: The rise of AI-powered credential theft and business email compromise. SlashNext Cybersecurity.https://www.slashnext.com
The support ticket system is for technical questions and post-sale issues.
If you have pre-sale questions please use our chat feature or email information@mile2.com .
Mile2 Cybersecurity Certifications is a world-leader in providing accredited education, training, and certifications for INFOSEC professionals. We strive to deliver the best course ware, the strongest Cyber Range, and the most user-friendly exam system in the market.
Our training courses follow our role-based Certification Roadmap. Plus, many of our classes include hands-on skill development in our Cyber Range. We train students in penetration testing,disaster recovery, incident handling, and network forensics. Additionally, our Information Assurance training certification meets military, government, private sector and institutional specifications.



